Opportunistic TLS
We had to upgrade our mail gateway/anti-spam software on Sunday because one of our vendors requires us to use encryption when exchanging emails with them. The easiest solution is to use opportunistic TLS, where the server will always try to connect to the other server using the TLS protocol. If the other server supports TLS, then traffic is encrypted. If not, then the email is sent using just regular SMTP without encryption.
This is actually the first time I’ve even heard of opportunistic TLS, I’m used to seeing S/MIME and PGP when reading about email encryption. What I like about this is encryption/decryption is done on the server side so the users don’t have to do anything different when sending emails and we don’t have to issue a certificate to each user and manage the keys.
If you’re using Exchange Server 2007, opportunistic TLS is already enabled by default. You can check this by entering Get-SendConnector “Send Connector Name” | Format-List in the Exchange Management Shell. Look for the IgnoreStartTLS parameter, if it’s set to false then opportunistic TLS is enabled.
To check whether a server supports TLS, telnet to the server on port 25 and check if the server supports the STARTTLS command, for example:
telnet mail.global.frontbridge.com 25
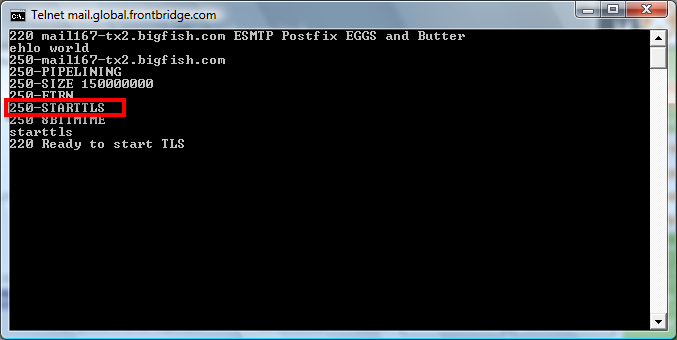
This server supports TLS
Here’s an example of the header of an email that was delivered with TLS enabled (I modified the IP addresses and names for privacy reasons):
Received: from mailgateway01 (1.2.3.4) by mailserver01.domain.com (1.2.3.5)
with Microsoft SMTP Server (TLS) id 8.1.263.0; Mon, 16 Mar 2009 18:05:18
-0400
Received: from mail.global.frontbridge.com ([65.55.88.22]) by mail.somedomain.com
([1.2.3.4]) with ESMTP (TREND IMSS SMTP Service 7.0; TLS:
TLSv1/SSLv3,128bits,AES128-SHA) id 06456c96000057da for <jdoe@microsoft.com>;
Mon, 16 Mar 2009 18:05:16 -0500
Tags: security, sysadmin, tech, networking
