Cracking passwords using the power of your GPU
I read this article a few weeks ago and I just had to try it. The use of GPUs in high performance computing is becoming very popular nowadays because you get so much computing power at very little cost compared to CPUs. You can pretty much buy a workstation and put 8 NVIDIA Tesla GPU cards in it and you got yourself a nice little supercomputer that can compete with a big CPU cluster or grid.
You not only save money on the hardware, but also on storage cost (a rack of servers vs. a workstation under your desk), electricity cost (go green!), and manpower to maintain and manage the cluster or grid computing environment.
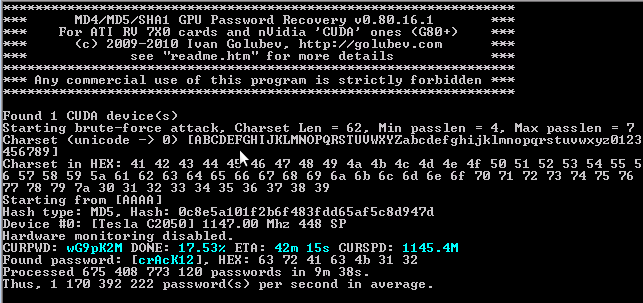
IGHashGPU, written by Ivan Golubez, is a great example of this. This application does a pure brute-force of a password hash to retrieve its original value. It supports multiple hashing algorithms, such as MD4, MD5, and SHA-1, and can run on multiple GPU cards in parallel.
The application also allows you to specify options, such as the minimum and maximum length of the original password and whether the password contains uppercase and lowercase characters, numbers, and special characters to speed up the process. For example, if you know that there’s a password policy of at least 6 characters then you can save time by setting the minimum length to 6 so the brute-force will start at 6 characters which will save some processing time.
I tested this application on a box that has one Tesla C2050 GPU and cracking a 7-character MD5-hashed password containing numbers, uppercase, and lowercase characters took a mere 9 minutes and 38 seconds at a rate of roughly 1.17 billion comparisons per second!
I haven’t tested this on a CPU but according to the article it would take about 4 days on the CPU. Pretty cool!
